Domain Spoof Test
Email domain spoofing allows attackers to send messages that appear to come from your organization. Without properly configured email authentication protocols like SPF, DKIM, and DMARC, your domain may be vulnerable to spoofed email attacks and business email compromise (BEC).
Can Your Email Domain Be Spoofed?
Are you aware that one of the first things hackers try is to see if they can spoof the email address of your CEO? If they are able to commit "CEO Fraud", attackers can more easily launch business email compromise (BEC) or executive impersonation attacks.
Now they can launch a "CEO fraud" spear phishing attack on your organization, and that type of attack is very hard to defend against, unless your users are highly ‘security awareness’ trained. Once cybercriminals know they can spoof any email address, this is the next thing they do:
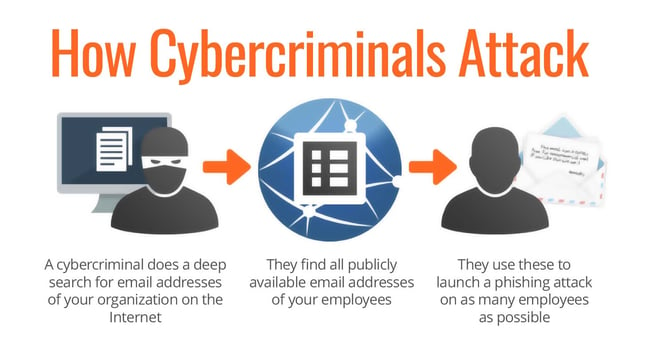
Once they have all publicly available email addresses, the fun starts. The more of your email addresses that are floating out there, the bigger your attack footprint is, and the higher the risk is. It’s often a surprise how many addresses are actually out there. Now they can send all employees an email supposedly coming from Human Resources, the CEO or perhaps the mail room, and social engineer your users to click on a link. Would you like to know if hackers can spoof your domain?
How the Domain Spoof Test Works
The Domain Spoof Test (DST) is a free, one-time assessment designed to determine whether your email domain can be spoofed by attackers.
Here’s how it works:
- Submit your domain for testing
- Provide the domain you want evaluated to initiate the assessment.
- We evaluate your email authentication configuration
The test reviews publicly available email authentication settings, including SPF, DKIM, and DMARC records, to determine whether your domain may be vulnerable to spoofing.
Receive your results and recommendations
You’ll get a summary of findings that identifies potential configuration gaps and guidance on how to strengthen your email authentication to reduce spoofing risk.
This assessment helps you understand whether attackers could impersonate your domain in phishing or business email compromise (BEC) attacks, so you can take corrective action before it’s exploited.
Sign Up For Your Free Domain Spoof Test
Find out now if your domain can be spoofed. The Domain Spoof Test (DST) evaluates whether your email domain can be spoofed and identifies potential mail server configuration issues. This free assessment helps you determine if SPF, DKIM, and DMARC protections are properly configured. You can request to get this DST, so you can address any mail server configuration issues that are found.
NOTE: Not everyone is qualified for the DST. It is not for individuals, but only for the person in the organization responsible for email security. We need a valid email address from the domain of your own organization, so Gmail, AOL, Yahoo or any other ISP are not accepted.