January 2020 - Maze ransomware has gotten the attention of the FBI. A warning to U.S. companies about this attack in which the perpetrator steals data and then encrypts it to extort victims was issued. “From its initial observation, Maze used multiple methods for intrusion, including the creation of malicious look-a-like cryptocurrency sites and malspam campaigns impersonating government agencies and well-known security vendors,” states the advisory obtained by CyberScoop. The warning provides technical indicators to detect Maze ransomware and asks victims to give them information that could help find the hackers. The bureau requests things like bitcoin wallets used by the hackers and the complete phishing email they sent to the victim.
New "leakware" attacks differ from traditional ransomware attacks by threatening to steal and publish data online unless a ransom is paid. The problem is if you don't pay, you're risking continued attacks on those whose personal data was included in the breach. If you do pay, of course there's no guarantee the attackers won't sell the data to a third party and launch their own attacks. The City of Johannesburg and the State of Virginia are two victims of these types of attacks.
In the beginning, ransomware used to only look for office files. Then backups became a secondary victim. Now, according to researchers at Kaspersky, attackers are looking for ways to directly target the NAS devices that host an organization's backups. It makes sense to cybercriminals, their goal is to make an organization feel their only option is to pay the ransom.
Encryption isn't the only problem when it comes to ransomware, there are many other nasty issues. Ransomware threat actors are doing more analysis, taking the time to maximize the potential damage and payoff. First, they discover which resources are organization’s crown jewels. What if suddenly encrypted would cause the most panic, pain, and operational disruption? Second, they find out how that data is backed up and what they can do to interfere with that process. They also know how many days of backup corruption they need, meaning they are getting better at encrypting backup data while it's online before it gets moved offline. Hackers are now stealing the crown jewel data and threatening to leak it unless the ransom is paid, so even if you do get it back it's still in their hands. Data-stealing ransomware has become so common that it has its own subclass known as data-theft ransomware. See more about how ransomware has become much worse!
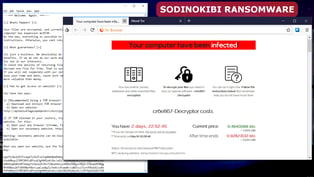
Travelex, a foreign-currency exchange company, was hit by the REvil/Sodinokibi actors on New Year's Eve. Its network data was encrypted and their customers were unable to take orders. REVil is said to exfiltrate data before encrypting the network as an added extortion incentive for victims to either pay or have the possibility of their data going public. A resulting cascade of nasty consequences for the victims include disclosure of PII, thus triggering data breach reporting requirements and the resulting governmental and third party legal headaches, potential crashing stock prices, fines, and the consequences of disclosure of confidential or proprietary information. REVil knows that large data breaches have sometimes resulted in crashing stock prices of up to 6%. Travelex later had to warn its customers to be on the lookout for phishing scams in an update on its corporate holdings website.
Phobos ransomware has been around since late 2017 and has morphed into a few strains, always targeting large organizations in hopes of getting a bigger payoff. It works to kill processes that may pose a threat, deletes Volume Shadow copies, disables Windows firewall, and prevents systems from booting into recovery mode. The real threat is on hw it's distributed as a Ransomware-as-a-Service business model. Threat actors using Phobos today are less experienced and therefore there are delays when negotiating ransom, and there is potential for issues around decryption since they themselves have no control over the malware used in attacks.
Nemty ransomware creators are now extorting victims by threatening to publish data to a blog if they don't pay. While the idea of publicizing sensitive information is nothing new, the use of a blog could add credibility to their claim of being willing to post the data (prospective victims can simply navigate to it to see previous victim’s data).
More new features have been added to the Ryuk strain, it now uses the Wake-on-Lan feature to turn on powered-off devices on a large compromised network to have greater success in encrypting them. In conversations with BleepingComputer, Vitali Kremez, Head of SentinelLabs, stated that this evolution in Ryuk's tactics allow a better reach in a compromised network from a single device and shows the Ryuk operator's skill traversing a corporate network. It's also now able to hack Active Directory and infect a larger number of machines. Ryuk Stealer, another version of this malware, uses new keywords and filetypes to automatically find an organization's most valuable data that they can extort and get their ransom.
Microsoft end-of-support for Windows 7 means systems will remain unpatched, creating an opportunity for future ransomware attacks to wreak havoc. If you remember 2017's WannaCry, it was successful because of unpatched systems. So three things you can do to protect against this possibility are: update your OS, ensure continual updates, and educate your employees to avoid becoming victims by clicking on phishing emails.
The FDIC issued a warning about heightened cybersecurity risks, urging banks to immediately shore up cybersecurity controls and technology safeguards against ransomware due to increased geopolitical tension. potential attacks that can only be assumed to be the result of relations between the U.S. and Iran. According to the FDIC, two specific attack vectors were mentioned: the use of malware-infected storage devices like USB drives and phishing/spear phishing attacks against users.
New EFS ransomware uses the Windows Encrypting File System (EFS) built-in encryption abilities against itself, not needing to download a payload executable that performs the encryption. SafeLabs researchers tested out three major AV solutions against EFS ransomware and found all three to failed to stop an attack. The news of this evolved tactic has antivirus vendors scrambling to provide updates to stop this ransomware in its tracks.
In Coveware's recently released Q4 Ransomware Marketplace Report, they found average cost of a ransom jumped from around $41K in Q3 of 2019 to just above $84K in Q4! Ransomware threat actors are targeting larger enterprise organizations in hopes of getting bigger payouts using sophisticated strains like Ryuk and Sodinokibi, while Ransomware-as-a-Service strains like Dharma, Snatch, and Netwalker are going after the small business sector.
Two senators of New York state recently proposed bills that would ban government agencies and local municipalities from using public money to pay cybercriminals ransom to get their files back. The first bill, proposed by Republican NY Senator Phil Boyle, and the second bill, proposed by Democrat NY Senator David Carlucci, are currently in committee. Several industry experts stated that this is the first time state authorities have proposed a law that outright bans paying the ransom all together.
Updates to FTCode ransomware targets the IDs and passwords on individual endpoints. Zscaler threat researchers have discovered new PowerShell code has been added to decrypt stored credentials from the following web browsers and email clients on Windows machines: Internet Explorer, Mozilla Firefox, Mozilla Thunderbird, Google Chrome and Microsoft Outlook. The repercussions are significant: In addition to holding data for ransom, attackers could lock users out of cloud-based applications, could use the newfound credentials to island hop, could provide access to Office 3656 via OAuth API access, commit CEO fraud scams, identity theft, and much, much more.
Anti-malware vendor Emisoft recently warned both private and public sector businesses that ransomware poses a real threat to the upcoming 2020 election - from campaign fundraising to promoting stories about candidates, the possibilities are endless. And, given the heightened political tensions that exist in the U.S., potential victims are already emotionally charged enough to respond to phishing and web-based attacks.
February 2020 - Having good backups in place may no longer completely save you from an attack. A new trend, exemplified by Maze ransomware, is for threat actors to exfiltrate an organization's data and use it to extort them. What this could mean for you is that your current cyber insurance may not cover you as well as you may think.
Threat actors behind Sodinokibi are promising black hat hackers an opportunity to "work with" the creators of REvil ransomware under "mutually beneficial conditions” in a hacking contest with a $15,000 prize. While competitions like this aren’t entirely new, this latest one boasting a five-figure prize is big news. The danger lies in the ability to foster ingenuity, spawn creativity, and encourage the sharing of ideas to make ransomware and other forms of malware more powerful amongst cybercriminals.
DoppelPaymer ransomware makes money from its victims, whether they choose to pay the ransom or not. While it's not the first strain to publicize a victim's stolen data if they don't pay, it goes a step further to work to sell the data stolen. This has turned ransomware attacks from a nuisance and an attack on operational productivity into a full-blown data breach, complete with remediation, legal, PR, etc. This extra step turns up the heat on organizations to simply pay the ransom.
EKANS ransomware is a relatively new variant that focuses on wreaking havoc on industrial control systems (ICS) and businesses that rely on it. EKANS attempts to disrupt operations by killing processes, then encrypting data, effectively holding both the organization’s production and data for ransom.
March 2020 - Talman Software, which is used by the majority of wool industry across Australia and New Zealand, was the victim of a ransomware attack that prevented brokers from being able to buy and sell wool.
Researchers at Quick Heal Security Labs have discovered a new strain of the “Mailto” ransomware nicknamed “Netwalker" that uses the art of deception to evade detection. It uses the debug API and Explorer.exe starts the execution, then proceeds to eliminate all of its traces when completed. According to Quick Heal Security Labs “the Mailto or Netwalker performs process hollowing in explorer.exe. This helps in evading the Anti-Virus software (AVs) to easily perform the encryption.
According to data protection vendor Datto’s director of channel development, Eric Torres, who spoke recently at the Xchange 2020 conference, MSPs are under greater attack today due to their direct and unlimited access to customer networks. Their recent Global State of the Channel
Ransomware Report shows that 85% of MSPs report their SMB customers experiencing ransomware attacks within the last 12 months.
Information Security Media Group (ISMG) reported that a growing number of ransomware groups are now exfiltrating data from their victims before deploying the ransomware. Brett Callow, a security researcher at Emsisoft, told ISMG that ransomware operators are also using this stolen data to craft targeted attacks against the compromised organization’s customers and partners. “We've now got pretty clear evidence that Maze et al. are using exfiltrated [data] to spear phish other companies,” Callow said. “The problem is, many companies do not disclose these incidents, so their business partners and customers do not know that they should be on high alert. Bottom line: more companies need to disclose, and to disclose quickly.”
Joel DeCapua, a special agent in the FBI’s global operations and targeting unit recently spoke at the 2020 RSA Conference in a session entitled Feds Fighting Ransomware: How the FBI Investigates and How You Can Help. In this session, attendees were able to get a sense of the severity of the problem of ransomware. According to DeCapua, a total of $144.35 million in ransoms were paid between January of 2013 and July 2019. The biggest “winners” in ransomware are: Ryuk – taking in $61 million, Crysis/Dharma – $24 million, Bitpaymer - $8 million, SamSam - $6.9 million.
Researchers at Lastline have come across a phishing campaign that uses Internet Query (IQY) files to bypass security filters and deliver a new version of the Paradise ransomware. Since it's a legitimate Excel file type, many organizations will not block or filter it but the file type can be leveraged to download an Excel formula (command) that could abuse a system process, such as PowerShell, cmd, mshta, or any other LoLBins (Living-off-the-Land Binaries). The researchers conclude that these files are difficult to flag since there’s nothing inherently malicious in them, so organizations need to focus on the URL.
According to security vendor Blackberry Cylance, Healthcare is the number 4 industry targeted for ransomware attacks. This data is corroborated by the latest numbers from insurer Corvus, who have released their latest Security Report on the state of Healthcare cybersecurity. According to the report, ransomware has risen consistently in 2019 over 2018, with a projection for Q1 of 2020 to be literally 12 times higher than the same quarter last year.
the Department of Homeland Security issued a warning that many organizations prepare for possible impacts of Coronavirus Disease 2019 (COVID-19), and consider alternate workplace options for their employees. The Infrastructure Security Agency (CISA) encouraged organizations to adopt a heightened state of cybersecurity. They also specifically noted that "Malicious cyber actors may increase phishing emails targeting teleworkers to steal their usernames and passwords."
U.K. cyberinsurer Beazley’s 2020 Breach Briefing covered some of the trends experienced by their customers between 2018 and 2019. According to the briefing: Business Email Compromise (BEC) was down slightly (12%) in 2019, Ransomware saw a massive increase of 131%, The top cause of loss (54%) was “hacking or malware”, Healthcare was the most targeted industry (35% of attacks), Small and Medium Businesses were the largest target (62%).
April 2020 - A new ransomware strain called 'Save the Queen’, distributes itself from its victim’s Active Directory Servers (known as Domain Controllers). Cybercriminals can do more with this access than simply encrypt data, and they may go even further than holding stolen data for ransom.
Three new ransomware families: Sodinokibi/REvil, Nemty, and DoppelPaymer are adopting the same style of “pay or we publish” tactic used by threat actors behind Maze ransomware. There are two big concerns here. The first is that organizations need to recognize that this will grow as a trend and, should they be attacked with ransomware, there are very few outs in that situation. Second, ransomware as an attack now must be considered a data breach; some subset of the organization’s data is stolen as part of the attack in order to both prove to the organization they have it, and will publish should the ransom not be paid.
Ransomware gangs have stepped up their attacks amid the pandemic to maximize their ill-gotten profits. Microsoft's Threat Protection Intelligence Team reported that almost every ransomware infection had evidence of attackers viewing and exfiltrating data. They also said there is a relatively long lag between compromise and ransomware deployment, and further, attackers often maintain control over endpoints after deploying ransomware.
May 2020 - New York Grubman Shire Meiselas & Sacks, media and entertainment law firm used by A-list stars, was hit by REvil ransomware. The firms website went down and threat actors behind REvil claim to have 756 gigabytes of data including contracts and personal emails. Cyber-security company Emsisoft says the hackers have posted images online of a contract for Madonna's World Tour 2019-20 complete with signatures from an employee and concert company Live Nation.
The total cost of the average ransomware attack more than doubles if the victim decides to pay the ransom, according to Sophos’s State of Ransomware 2020 report. According to the report, the average total cost of a successful ransomware attack—including downtime, technical recovery, extra hours, lost business, as well as the ransom payment—was $732,000 for victims that refused to pay the ransom. Interestingly, that number rises to $1,448,000 for organizations that do pay the ransom.
A new strain Ako ransomware is demanding one ransom payment to decrypt their data, and a second payment to not publish stolen files. This tactic appears to only apply to larger victim companies and is also dependent upon the kind of data stolen. While we’ve seen the average ransom doubling this year, this second demand for a ransom tends to run in the $100K to $2M range (remember, the organizations seeing these types of attacks are the ones the the Ako folks believe have deep pockets). This second ransom almost assures the cybercriminal some form of payment, one way or another.
Data from Coveware, a company that handles ransomware incidents, shows that the average ransom price increased from $84,000 in 2019 to $111,605 in the first quarter of 2020. Ryuk and REvil continue to be responsible for this increase in average ransom.
The ransomware formerly known as Mailto has rebranded as Netwalker and are conducting interviews to identify appropriate affiliates to work with. According to the details uncovered, affiliates receive up to 70% of the ransom, giving cybercriminal organizations ample incentive to partner up with Netwalker.
June 2020 - Recent changes in ransomware attacks that now include data theft for the purposes of extorting the ransom or face public posting of the stolen data recategorize ransomware as a data breach instead of simply a malware infection-turned-decryptor. And it’s this change in attack tactics that brings us to the issue of data breach notification. Most ransomware attacks now involve data exfiltration so now you need to determine whether data was stolen, what was taken, and whether you need to begin the notification process.
Brian Krebs had the news first. "The criminal group behind the REvil ransomware enterprise has begun auctioning off sensitive data stolen from companies hit by its malicious software. The move marks an escalation in tactics aimed at coercing victims to pay up — and publicly shaming those don’t. But it may also signal that ransomware purveyors are searching for new ways to profit from their crimes as victim businesses struggle just to keep the lights on during the unprecedented economic slowdown caused by the COVID-19 pandemic." You can count on other cyber organized crime gangs to follow this "innovation".
In Kivu's What Doxxing Victims Reveal About “Targeted Attacks” report, they analyzed the geographic and industry-based metrics of over 140 ransomware victims who were doxxed between February 1, 2020 and May 1, 2020. Among their key findings were: 55% of all doxxed victims were located or headquartered in the US, followed by 7% in the UK and 4% in France. The remaining 34% of victims were spread out across the globe. Companies that fall under the consumer sector were the most represented in the data at 30%. This was followed by 22% in industrials and 15% in financial services. Kivu’s investigation showed that ransomware variants generally do not favor one industry over another – rather, they are likely to deploy more successfully within certain environments, which are industry agnostic.
According to Microsoft’s Advanced Threat Analytics, the median number of days an attacker sits within your network undetected is 146 days. The new PonyFinal ransomware demonstrates this behavior. According to Microsoft, attackers in this case put a human touch on the attack, not leveraging automation, but are patient and are looking for victims of opportunity rather than trying to hit everyone and anyone. By first compromising internet-facing web systems, attackers compromise privileged credentials and use PowerShell tools and service accounts to obtain the needed access the victim network. In most cases, the attackers focus on endpoints where the Java Runtime Environment (JRE) is installed Then, according to Microsoft, attackers “stay dormant and wait for the most opportune time to deploy the [PonyFinal] payload.”
Researchers at Symantec have spotted a new element in recent Sodinokibi (aka REvil) ransomware campaigns, with the attackers scanning compromised networks for PoS software. It's possible that the attackers could be looking to scrape this information as means of making additional money from campaigns, either by directly using the payment information themselves to raid accounts, or to sell it on to others on underground forums.
Symantec issued an urgent warning that Russian hackers had exploited the sudden change in American work habits to inject code into corporate networks with a speed and breadth not previously witnessed using WastedLocker. The end goal of these attacks is to cripple the victim’s IT infrastructure by encrypting most of their computers and servers in order to demand a multimillion dollar ransom. At least 31 customer organizations have been attacked, meaning the total number of attacks may be much higher. The attackers had breached the networks of targeted organizations and were in the process of laying the groundwork for staging ransomware attacks.
July 2020 - Recent updates to the well-known Thanos Ransomware-as-a-Service make it a formidable challenge for even well-secured organizations. Some of the improvements include: RIPlace technique for avoiding detection, Encryption speed enhancements, Disabling of 3rd party backup solutions, Ability to impersonate Windows SYSTEM via process hollowing and FTP-based reporting.
TripWire recently revealed that more than 10% of ransomware infections now involve some element of data theft. These attacks involved numerous ransomware gangs. In March 2020, for instance, the Nefilim crypto-malware strain began telling its victims that it would publish their stolen data within a week unless they paid their ransom. That was about a month before the security firm learned of Ragnar Locker’s demand of 1580 bitcoin (approximately $11 million) as ransom from Energias de Portuga (EDP), a Portuguese electric utilities company from which the attackers claimed to have stolen 10TB of data. Approximately a month after that, DoppelPaymer published a new entry on its data leaks site for the City of Torrance, CA.
The Securities and Exchange Commission, through its Office of Compliance Inspections and Examinations (OCIE), issued a warning to advisors and broker-dealers to “immediately” review their cybersecurity controls to prevent and respond to an increase in phishing campaigns and ransomware attacks. The alert provides “observations to assist market participants in their consideration of how to enhance cybersecurity preparedness and operational resiliency to address ransomware attacks. We have observed registrants utilizing the following measures: Incident response and resiliency policies, procedures and plans, Operational resiliency, Awareness and training programs, Vulnerability scanning and patch management, Access management and Perimeter security.
According to security researchers at CheckPoint, the Phorpiex botnet – which first reared its ugly head back in 2018 appears to be experiencing a resurgence in interest last month. Estimated to have generated a half million dollars in revenue in 2019, Phorpiex has traditionally distributed ransomware, cryptominers, and malware to accomplish this. Phorpiex ranked second in global reach last month, affecting 2% of organizations globally, and even made their Top 10 malware families list for June.
The CONTI family of ransomware has taken steps to improve the performance of encryption while using new and old methods to ensure success. CONTI uses up to 32 independent threads to simultaneously encrypt data, thereby speeding up the process. According to new research from VMware, CONTI uses the Windows Restart Manager to cleanly close applications with locked files, allowing those files to be included in the encryption process. They avoid detection by using 277 unique string encoding algorithms to obfuscate the original code and bloat the simple program into a larger application that is more difficult to identify as the ransomware.
August 2020 - Coveware’s Q2 2020 Ransomware Marketplace Report shows that ransomware attacks are growing in sophistication, scope, effectiveness, and cost. According to the report: The average ransom payment has jumped form $111K in Q1 to $178K in Q2, The median company size has steadily increased from 25 in 2018 to 100 in Q2 and continues to increase “Big Game” variants like Maze targeted much larger companies, averaging over 16K employees, The top 3 ransomware players were only responsible for 30% of attacks in Q2, highlighting that many new variants are gaining steam, 30% of ransomware attacks involved a threat to release data (with no confirmation that data was actually stolen), 22% of attacks actually involved confirmed exfiltrated data – this is up from 8.7% in Q1, a rise of 152%, Both Maze and DoppelPaymer variants had multiple months in both Q1 and Q2 of this year where 100% of their attacks involved data exfiltration, Payment “defaults” (where data cannot be decrypted) remains low, at 2%.
A group of cybercriminals that helped a Ukranian ransomware gang launder more that $42 million over two years was arrested. This was accomplished with assistance from the Binance cryptocurrency exchange whose “Bulletproof Exchanger” project helped authorities identify large transactions and trace them back to individuals in the real world.
A new ransomware operation named DarkSide began attacking organizations earlier this month with customized attacks that have already earned them million-dollar payouts. But here is the clincher: When performing attacks, DarkSide will create a customized ransomware executable for the specific company they are attacking. DarkSide states that they only target companies that can pay the specified ransom as they do not "want to kill your business."The threat actors have also stated that they do not target the following types of organizations: Medicine (hospitals, hospices), Education (schools, universities), Non-profit organizations and the Government sector.
The FBI has arrested a Russian citizen (27-year-old Egor Igorevich Kriuchkov) for trying to recruit an employee of Tesla’s Gigafactory Nevada to plant malware inside the firm. According to the US Justice Department, Kriuchkov promised to pay as much as $1 million to the employee. The goal: to steal data from the company and then threaten to make the information public, unless a large (~$4million) ransom was paid. However, the Justice Department’s complaint suggests the employee ended up secretly working with the FBI to gather evidence against Kriuchkov, who was arrested on Saturday in Los Angeles.
The Australian Securities and Investments Commission (ASIC) is suing RI Advice Group for being hacked multiple times over a year’s time that includes 155 hours of undetected hacker activity. According to a notice filed earlier this month in Australian federal court, RI Advice Group was the victim of two remote access-turned-ransomware attacks in December 2016 and May 2017, and a third successful attack on a server containing sensitive financial information and client identification documents in December of 2017. Because RI Advice Group is a financial services firm, they are subject to the ASIC, who are suing them for failing to establish and maintain compliance measures that include security controls.
September 2020 - According to security researchers at Kaspersky in a guest blog post, the attack chain used by threat group DeathStalker seems to be intent on gathering sensitive business information rather than deploy malware, ransomware, or any other malicious action normally seen for financial gain. What makes this attack so interesting is the resourcefulness found in the details. According to the article, the Powersing attack includes some of these capabilities: A modified .LNK file is used as the malicious attachment that launched CMD.EXE, then PowerShell, An embedded decoy document is presented to the user while it continues its malicious actions to keep them from becoming suspicious, It uses drop dead resolvers – URLs that point to posts or content in legitimate sites that contain Base64 encoded strings, such as the following.
According to AD-focused cybersecurity vendor Semperis, in their Recovering Active Directory from Cyber Disasters report, it appears the IT organizations simply aren’t prepared: 84% of orgs feel an AD outage would be “significant, severe, or catastrophic”, Only 3% of orgs are “extremely confident” about their ability to recover AD to new servers should it be necessary, Only 15% of organizations have actually tested their AD recovery plan in the last six months.
According to new research from Checkpoint, the new version of the Qbot trojan contains a number of collector modules. One is used to harvest browsing data, email records, and banking credentials. Another uses mimikatz to scrape RAM for credentials. And still another new module seen by Checkpoint, extracts specific email threads related to tax payments, job recruitment, and COVID-19 from the endpoint’s Outlook client, uploading them to the attacker's command-and-control (C2) server.
New data from cyber insurer Coalition shows massive increases in both the frequency of ransomware attacks and the ransom demand with Maze and Ryuk leading the way. Their H1 2020 Cyber Insurance Claims Report points out the increases are more than just anecdotal. According to the report in the first half of 2020: Ransomware attack frequency increased 260%, Ransom demands increased 47%, Maze and Ryuk ransomware variants represented 53% of all attacks and Ransoms ranged from $1000 to over $2,000,000. Further, the report found that funds transfer fraud has increased 35% since the onset of COVID-19. Most funds transfer fraud claims involve the following social engineering techniques: Invoice Manipulation – This usually involves either using a compromised third-party email or having specific pending transaction details enough to fool the victim. Look-alike Domains – Impersonation is often used where the cybercriminal uses a domain with an added/subtracted/swapped character in the name to trick the victim into believing the email requesting funds is legitimate. Email Spoofing – This is the simplest form, as in the CEO credit card scam (where the email purports to be from the CEO’s personal email address). Sometimes just looking like it *could* be from someone legitimate is enough to fool the victim.
October 2020 - BitDefender’s recent Mid-Year Threat Landscape Report 2020 shows that the first half of 2020 saw a 7x jump in the frequency of ransomware attacks when compared to the same time in 2019. We’ve also seen ransoms jump by an average of 60 percent this year, signaling that cybercriminals are keenly aware of what the havoc they’ve wreaked is worth to an infected organization.
The US Treasury Department's Office of Foreign Assets Control (OFAC) has sanctioned multiple ransomware criminals over the last few years, most notably the Russian cybercrime syndicate aptly named Evil Corp. However, not only Eastern European hackers were sanctioned, various North Korean and Iranian actors are also on the list. In an advisory published on Oct 1st, 2020 OFAC made it clear to U.S. companies that paying millions of dollars of ransoms to those groups will invite hefty fines from the federal government. Those that run afoul of OFAC sanctions without a special dispensation or “license” from Treasury can face several legal repercussions, including fines of up to $20 million.
The Wall Street Journal reported that U.S. prosecutors charged six Russian intelligence officers who are accused of engaging in the most destructive cyber attacks of recent years. Notable attacks include operations that knocked out Ukraine’s energy grid, exposed emails from the French president’s party and damaged systems all over the world in the extremely costly 2017 NotPetya ransomware attack. The defendants are charged with several counts including conspiracy, computer hacking, wire fraud and aggravated identity theft.
Security vendor Digital Shadows’ Quarterly Update: Ransomware Trends In Q3 highlights their findings of more and more ransomware attacks turning into data breaches: Maze, DoppelPaymer, and Sodinokibi made up 80% of alerts of the leak sites, Conti and NetWalker ransomware groups joined the ranks of those hosting a leak site and The number of leak sites by well-known ransomware groups rose to 7 by the end of Q3.
November 2020 - In a new report from Security Researcher Vitali Kremez puts the spotlight on exactly how the group behind Ryuk ransomware is successful in infecting and obtaining payment from its victims. The most shocking finding was that the largest ransom paid was 2200 BTC (just under $34 Million USD)!
In Datto’s Global State of the Channel Ransomware Report, they found that the SMB is just as much a target of opportunity as the enterprise. And in many cases, despite it being impactful to the business, SMB’s simply aren’t aware of the danger. According to the report: 70% of MSPs report ransomware as the most common malware threat to SMBs, Only 30% report that their clients feel ‘very concerned’ about ransomware, 62% of MSPs said clients’ productivity was impacted due to attacks and 39% said their clients experienced business-threatening downtime.
Unlike the traditional methods of notifying victim organizations by simply taking over a computer or providing a “readme” text file, this new method has some devilish benefits. Egregor ransomware victims have experienced print jobs being sent to every available printer that notify the reader that all computers and servers are locked, data has been stolen, and “next steps” to take to rectify the situation.
December 2020 - According to researchers at Atlas VPN the average ransomware payout has increased by 178% over the past year. In Q4 2019, the payments averaged $84,000. By Q3 2020, the average payment had risen to $234,000. These numbers have steadily increased each quarter. Atlas VPN offers the following advice for organizations to defend themselves against these attacks: “Firstly, employees should follow well-known cybersecurity practices, such as using 2-Factor Authentication (2-FA) whenever possible, not clicking on suspicious links, and updating their software and OS. These steps might seem like basic practices, but surprisingly, many people do not follow them. “Employers should set up employee training workshops where a security specialist shares security practices together with scenarios that could happen if these tips are not followed. Showcasing incidents that already happened in other companies could be of value to show employees how a single malicious link can cripple a company.”
Some ransomware gangs are now cold-calling victims on their phones if they suspect that a hacked company tried to restore from their backups to avoid paying ransom demands. Ransomware groups that have been seen calling victims in the past include Sekhmet (now defunct), Maze (now defunct), Conti, and Ryuk, a spokesperson for cyber-security firm Emsisoft told ZDNet on Thursday. These phone calls are another escalation in the tactics used by ransomware gangs to put pressure on victims to pay ransom demands after they've encrypted corporate networks.
UK cyber insurer Beazley, both the extortion demand amounts and total cost of ransomware payments have increased an average of 100% from 2019 to 2020. According to Beazley, a number of best practice steps exist to better protect against ransomware that include proper backups of key systems and data, email filtering and user education.