What is Spear Phishing?
Spear phishing is a more targeted form of phishing. A majority of successful data breaches start with a spear phishing attack. Get the information you need to defend against this threat.
Spear Phishing Definition
Spear phishing is an email targeted at a specific individual or department within an organization that appears to be from a trusted source. It's actually cybercriminals attempting to steal confidential information.
How Does Spear Phishing Work?
You may be wondering what it takes to send this type of attack. This is not trivial, and can only be done by someone trained in advanced hacking techniques. We will first take a look at the steps required to send an attack, and then we’ll look at steps to mitigate this threat.
We will try to keep this as non-technical as possible, but there will be a few terms you may have to look up. Here are the 6 steps:
1. Identify Email Addresses
There are two ways hackers send phishing campaigns: the first is ‘spray-and-pray’ which is a shotgun approach. Get as many email addresses from the organization they can, and send them all an email that they might click on. The second approach is decide what data you are after, then figure out who has access to that data, and specifically target those people. That is the spear phishing approach, and for instance LinkedIn is extremely useful during this targeting step.
There are several ways to get your hands on the email addresses from an organization. The one favored by cybercriminals is using scripts to harvest email addresses from the large search engines. You’d be surprised how many emails can be captured this way and how big a given organization's spear phishing attack surface is. Once they have the email addresses of the few people they are targeting, it's on to step two.
2. Antivirus Evasion
For an attack to arrive in the inbox of a target, the email needs to get past the antivirus software that the target uses. A quick search on the IT job sites for open system admin positions at the target's organization provides an astounding amount of information. They will often list exactly what antivirus and which version they use. Otherwise DNS cache snooping and even social media give many other ways to find out. Once the AV is known, it's installed on a test bed to make sure the email comes through ok. Metasploit can help with this, it is an open source computer security project which provides information about security vulnerabilities and aids in penetration testing.
3. Egress Filtering
Hackers can't get the information out of the organization they are attacking unless the payload sent with the attack allows traffic to exit the organization. A popular payload is called ‘reverse_https’ because it creates an encrypted tunnel back to the metasploit server, which makes it very hard for security software like intrusion detection or firewalls to detect anything. For those products, exiting phishing data all looks like normal https traffic.
4. Spear Phishing Scenario
There are many articles written about this by now, and it’s the essence of social engineering users. If they haven’t had high-quality security awareness training they are easy targets for spear phishers. The attacker does research on their targets, finds out who they regularly communicate with, and sends a personalized email to the target that uses one or more of the 22 Social Engineering Red Flags to make the target click on a link or open an attachment. Just imagine you get an email from the email address of your significant other that has in the subject line: Honey, I had a little accident with the car, and in the body: I took some pictures with my smart phone, do you think this is going to be very expensive?”
5. Sending The Emails
One option is to raise a temporary mail server and blast away, but that mail server will not have a reputation score which will block a lot of email from getting in. A better solution is going to GoDaddy, purchasing a valid domain name, using the free email server that comes with the domain and set it up, so that an MX record is automatically created by GoDaddy. Also it's easy to change the GoDaddy Whois information to match any targeted domain. All that helps mail getting through, which can be sent with any email client, or with a script.
6. Harvesting Treasure
Let’s assume a target clicked on the link, and cybercriminals were able to place a keylogger on their machine. Now it’s a matter of waiting for the hourly burst of keyboard data back to their server, and monitoring for the credentials they are after. Once they have those, it’s a matter of getting into the workstation, getting all network password hashes, cracking them and getting elevated to administrator access to the whole network.
Did you know that 91% of successful data breaches started with a spear phishing attack?
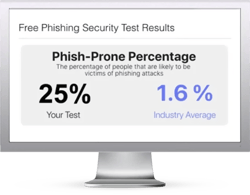
Find out what percentage of your employees are Phish-prone™ with your free phishing security test. Plus, see how you stack up against your peers with the new phishing Industry Benchmarks!
Here's how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Start phishing your users now.
Fill out the form, and get started immediately!
Real World Examples
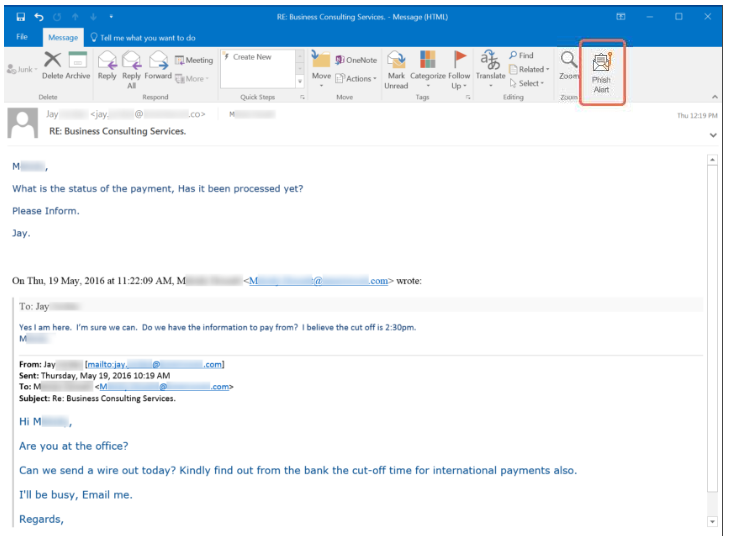
Here's an example of a KnowBe4 customer being a target for CEO fraud. The employee initially responded, then remembered her training and instead reported the email using the Phish Alert Button, alerting her IT department to the fraud attempt.
When the employee failed to proceed with the wire transfer, she got another email from the threat actors, who probably thought it was payday. Although they never specified a requested amount of money to transfer in this case, the company stood to lose a significant chunk of change.
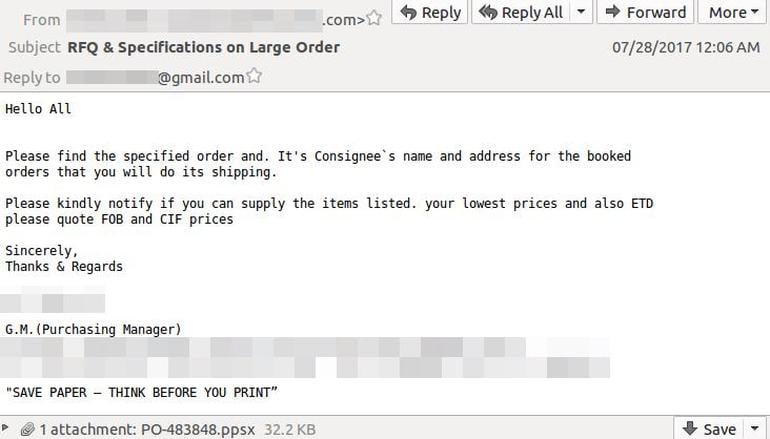
Cybercriminals are exploiting a Microsoft vulnerability to bypass endpoint security software and deliver the Remcos remote access Trojan via Microsoft PowerPoint decks.
The attack begins with spear phishing email, claiming to be from a cable manufacturing provider and mainly targets organizations in the electronics manufacturing industry.
The sender's address is spoofed to look like a message from a business partner and the email was written to look like an order request, with an attachment containing "shipping information". Here is how it looks:
Many spear phishing attacks contain a ransomware payload. Defray ransomware is just one example of a strain that targets healthcare, education, manufacturing and tech sectors in the US and UK. The infection vector for Defray is spear phishing emails containing malicious Microsoft Word document attachments, and the campaigns are as small as just a few messages each.
Once opened, the attachment installs the ransomware. It has only been seen in small, very targeted attacks and demands a high ransom of $5000. The image to the right is what the document looks like.
Phishing vs. Spear Phishing
While phishing and spear phishing attacks are similar, there are many key differences to be aware of. A phishing campaign is very broad and automated, think 'spray and pray'. It doesn't take a lot of skill to execute a massive phishing campaign. Most phishing attempts are after things like credit card data, usernames and passwords, etc. and are usually a one-and-done attack.
On the other hand, spear phishing is highly targeted, going after a specific employee, company, or individuals within that company. This approach requires advanced hacking techniques and a great amount of research on their targets. Spear phishers are after more valuable data like confidential information, business secrets, and things of that nature. That is why a more targeted approach is required; they find out who has the information they seek and go after that particular person. A spear phishing email is really just the beginning of the attack as cybercriminals attempt to get access to the larger network.
Here's an infographic highlighting the differences between phishing and spear phishing.
How To Prevent Spear Phishing Attacks
Now, how to mitigate against attacks like this? There is no single approach that will stop this threat, but here is what you need to do to be a hard target for criminals:
- First of all, you need all your defense-in-depth layers in place. Defending against attacks like this is a multi-layer approach. The trick is to make it as hard as possible for the attacker to get through and to not rely on any single security measure to keep your organization safe.
- Do not have a list of all email addresses of all employees on your website, use a web form instead.
- Regularly scan the Internet for exposed email addresses and/or credentials, you would not be the first one to find one of your user’s username and password on a crime or porn site.
- Never send out sensitive personal information via email. Be wary if you get an email asking you for this info and when in doubt, go directly to the source.
- Enlighten your users about the dangers of oversharing their personal information on social media sites. The more cybercriminals know, the more convincing they can be when crafting spear phishing emails.
- Users are your last line of defense! They need to be trained using new-school security awareness training and receive frequent simulated phishing emails to keep them on their toes with security top of mind. We provide the world's largest content library of security awareness training combined with best in class pre- and post simulated phishing testing. Since 91% of successful attacks use spear phishing to get in, this will get you by far the highest ROI for your security budget, with visible proof the training works!
...and ALWAYS remember to Think Before You Click!
Resources
Phishing Security Test
Domain Spoof Test
Do your users know what to do when they receive a suspicious email or attachment?