KnowBe4's new scientifically-based assessments help you tailor training to address proficiency gaps and weaknesses, as well as monitor the impact your security awareness training program has on improving your users knowledge and sentiment to security awareness.
Find out where your users are regarding both security knowledge and security culture to help establish baseline security metrics you can improve over time. Assessments help you to identify users that have a higher proficiency in security in not only knowing the right thing to do but also actually doing the right thing as part of the security culture you’re trying to achieve in your organization.
You now have the ability to send a skills-based assessment and a security culture survey to your users from your KnowBe4 platform. You can use the assessments and surveys to monitor over time how successful your security awareness training program increases your users’ security knowledge and sentiment to a security-aware culture.
Finally, you have a way to measure what your users know and how much they care when it comes to applying your awareness training, and continue to manage and build a mature security awareness program.
KnowBe4's Security Awareness Proficiency Assessment (SAPA) is grounded in the latest assessment science research and seeks to assess your users’ susceptibility to cyber attacks, and more specifically, their susceptibility in relation to your organization’s specific cyber security needs.
The assessment is designed to help your organization determine your security awareness training needs by identifying gaps in individual users’ knowledge as well as recommended learning improvements. The assessment provides metrics to improve your users’ security awareness knowledge over time while also helping you tailor and target the right training campaigns across your organization to the right users at the right time.
You can use assessment results to identify high-risk users and deliver targeted training to those users with automatic enrollment through the use of Smart Groups. Your users will be presented with 23 random questions about security awareness from a much larger question bank. This ensures each user’s assessment is unique and that they won't be able to share answers with their coworkers, which would result in inaccurate reporting.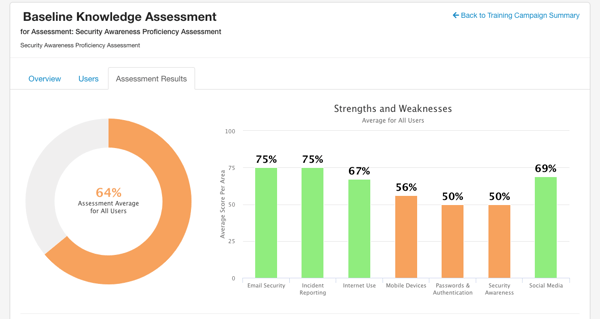 SAPA measures and scores your users across seven knowledge areas which include:
SAPA measures and scores your users across seven knowledge areas which include:
The Security Awareness Proficiency Assessment Methodology:
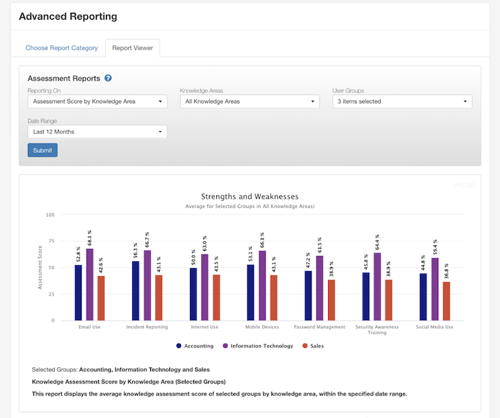
 SAPA Benchmarks lets you compare your organization’s security awareness proficiency scores with other companies in your industry. When you use SAPA, get a firsthand look at how your organization stacks up across the seven security knowledge areas from your baseline assessment as well as monitor your organization’s improvement over time.
SAPA Benchmarks lets you compare your organization’s security awareness proficiency scores with other companies in your industry. When you use SAPA, get a firsthand look at how your organization stacks up across the seven security knowledge areas from your baseline assessment as well as monitor your organization’s improvement over time.
See where you stack up! With regular phishing security tests, awareness training, and proficiency assessments, you’ll see how your Human Firewall improves over time helping to reduce risk and improve your IT security defense.
Building a strong and positive security culture is an effective mechanism to influence your users’ behavior and thereby reduce your organization’s risk. Security culture can be defined as the ideas, customs and social behaviors that impact the security of your organization.
The Security Culture Survey will help you answer questions like:
In addition to answering operational questions like those above, the SCS provides you with a KPI for reporting your organization’s security posture to the board.
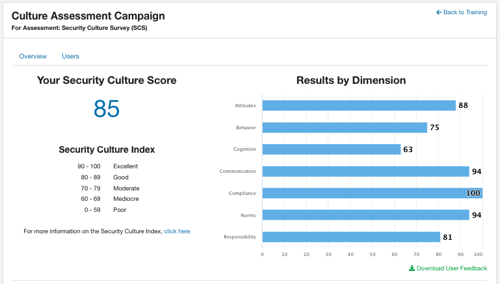
The Security Culture Survey measures the sentiments of your users towards security in your organization – the psychological and social aspects that drive social behavior. Specifically, the SCS measures seven dimensions of security culture which include:
The survey helps you measure and manage your security culture by giving you individual and aggregated culture scores that show a precise picture of the security landscape of your users and organization. Further analysis and reporting provides you with insights on which areas need improvement and what to focus on next, with recommended takeaways based on your culture score.
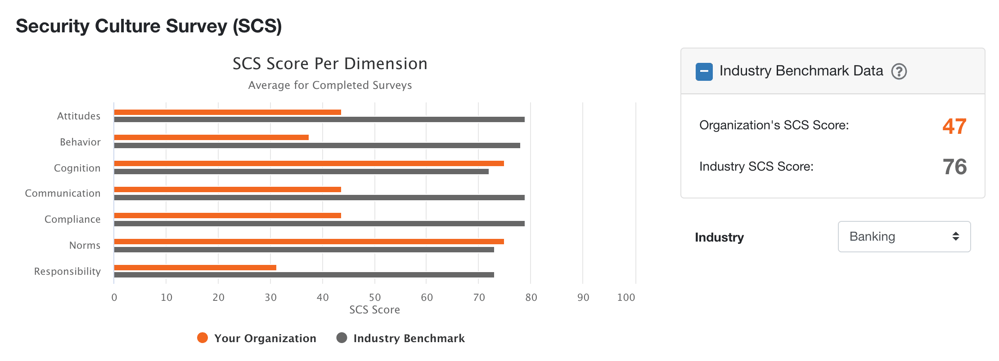
The SCS gives you a research-driven measurement instrument to show you the overall effectiveness of your security culture program and how your security culture improves over time. The SCS measures the seven dimensions of security culture: attitudes, behaviors, cognition, communication, compliance, norms, and responsibilities.
Security culture metrics do not measure security awareness training completion rates or phishing assessments, rather they serve the purpose of measuring security culture which can only be adequately measured via a scientific approach. The SCS integrates a scientific method of measuring and a scientific method of prediction to provide evidence-based results that enables you to assess, build, and improve your organization’s security culture.
Security culture metrics allow organizations to assess the true nature of their security culture and its components, and to compare such assessments within organization across departments/teams and between various organizations, thereby providing a baseline for benchmarking security culture.
The scientific method of prediction is based on advanced statistical algorithms (such as structural equation modeling, multilevel modelling and big data approaches) and allows KnowBe4 to identify correlations between elements of an organization's security culture and employee behavior. As security culture data is gathered over repeat measurements, organizations will be able to leverage the power of this prediction engine to improve the effectiveness of security culture change.
Security Culture Survey Methodology:
Measuring culture requires a scientific approach. The development of the metrics used in the SCS followed a strict scientific procedure repeated over time, which allows us to claim that measures are valid and reliable – in other words, that they are measuring what they intend to measure and are valid instruments for obtaining true (or reasonably accurate) information about reality. These steps include:
Items were evaluated for clarity, readability, social desirability bias by experts trained in survey design and item development. Exploratory and confirmatory factor analytical procedures using the R software package were used to confirm the seven-dimension structure of the security culture concept. Additional analyses were performed to confirm discriminatory and convergent validity of security culture concept. Analysis of Cronbach’s alpha (used as an estimate of reliability) on all seven dimensions of security culture proves that the metrics used are internally consistent.
In addition to the important mechanisms described above, several other mechanisms are employed that include:
More information about the scientific approach used to develop and test the Security Culture Survey is available in the research report, "The 7 Dimensions of Security Culture" published by CLTRe (a KnowBe4 company).
The SCS Benchmarks lets you compare your organization’s average security culture score with other organizations in your industry. When you use the SCS, you get an overview of the seven dimensions that make up your security culture and an overall security culture score for your organization. You can use the SCS Benchmarking to track how your organization’s culture changes over time relative to your specific industry.
See these new features and more for yourself, request a product demonstration today!