SynoLocker appeared in August 2014. Unlike the others that targeted end-user devices, this one was designed for Synology network attached storage devices. And unlike most encryption ransomware, SynoLocker encrypts the files one by one. Payment was 0.6 Bitcoins and the user has to go to an address on the Tor network to unlock the files.
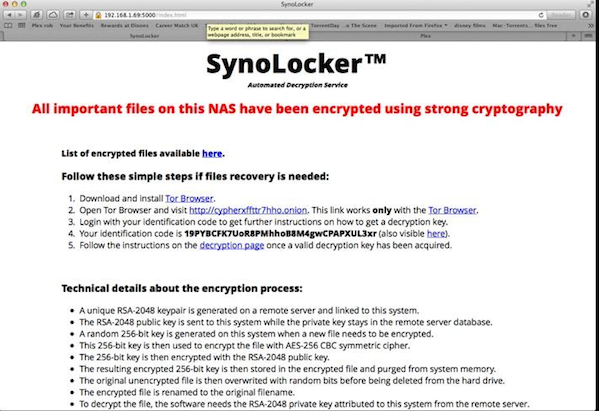
Unlike other ransomware viruses, SynoLocker encrypts the files stored on the NAS, and modifies the admin web page to a screen that is demanding a Bitcoin ransom to be paid only through Bitcoin over a Tor network. It also is very similar to Cryptolocker: Its payment system is very similar, but most importantly is its choice of encryption algorithms and parameters. SynoLocker malware also disables access the system using SSH and Telnet. The depth and the magnitude of this particular ransomware virus are still unknown, as experts try to unearth whether or not it is a serious threat. Another reason for the confusion is that the Synology network is the SynoLocker's biggest priority. As of yet, Synology has not patched the vulnerability. Whether the malware exploits 0day vulnerability in the operating system (DSM) or exploits devices with poor credentials or an outdated system (versions prior to 5.0 have serious known vulnerabilities) is unknown at this time. Until the patch is started and completed, we suggest that users of Synology devices limit their accessibility via the internet L 443,21,23,22,5000,5001 and 80. And a rule of thumb for every organization is to keep an off-line backup.
