Ransom32 is the first Ransomware-as-a-Service (RaaS) that was fully developed in Javascript, HTML and CSS. That's significant because it can be easily repackages to infect Linux and MacOS X and is a step closer to a "write-once-infect-all" threat although it's only currently targeting Windows. Javascript is a scripting language used by web browsers, disabling it would mean breaking most interactive features across the web.
Ransomware-as-a-Service has become a popular model amongst cybercriminals. The way this one works is anyone can access theit darkweb TOR site, register with a Bitcoin address, then customize and download their own version of the malware. The original developers take a 25% cut of any ransom collected, the rest goes to their criminal affiliate. Affiliates have a console available where they can view statistics and update settings on their personal ransomware campaign.
Affiliates can choose how to distribute Ransom32, whether through spray and pray phishing campaigns, more targeted spear phishing, malvertising, manually hacking linux servers or brute forcing terminal servers.
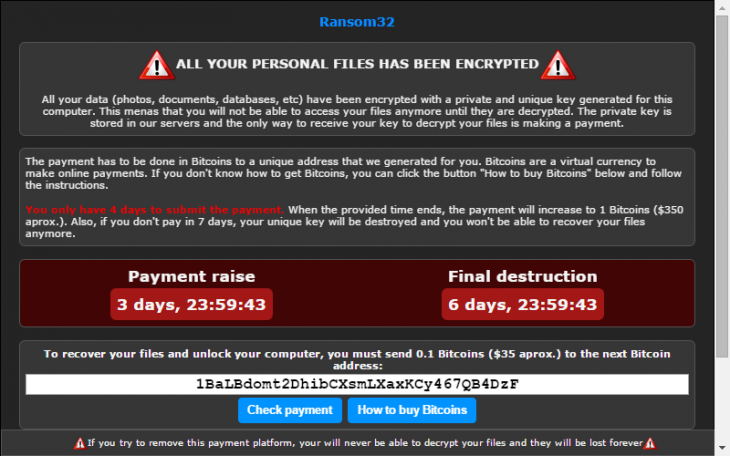
When this executable is run, it extracts several files and creates a shortcut in the start menu and the ransomware will start at login. The shortcut points to a chrome.exe executable that is actually a NW.js package that contains Javascript code that will encrypt the victim's data and then display a ransom note:
NW.js allows node.js, standard JavaScript scripts, and chromium to be bundled into a single executable. When that executable is run, Chrome aunches the JavaScript scripts. This allows any whitehat or blackhat developer to create and distribute native apps that run just like a normal executable.
Because NW.js is actually a legitimate framework and application files can be encrypted quietly and the malware package is more difficult to detect. Ransom32 only encrypts certain file extensions using AES encryption, but it will use extensions like .*sav* that will encrypt all files containing that string.
At the time there is no known decryption for Ransom32 but we will update this page if one becomes available.
