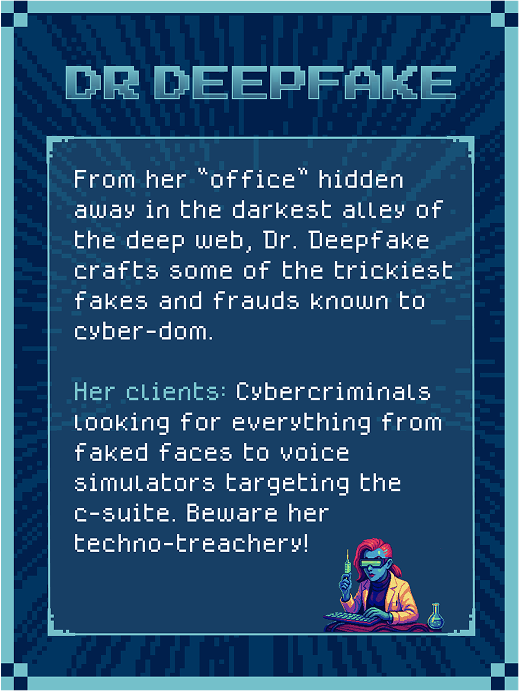
FAIK Everything: The Deepfake Playbook, Unleashed
Watch this heart-stopping webinar where Perry Carpenter, KnowBe4's Chief Human Risk Management Strategist, rips the mask off the alarming rise of AI-powered social engineering. Whether you're a security leader, red teamer, risk manager, or anyone responsible for keeping your organization safe in this brave new world, this session is your ticket to staying ahead of the curve.