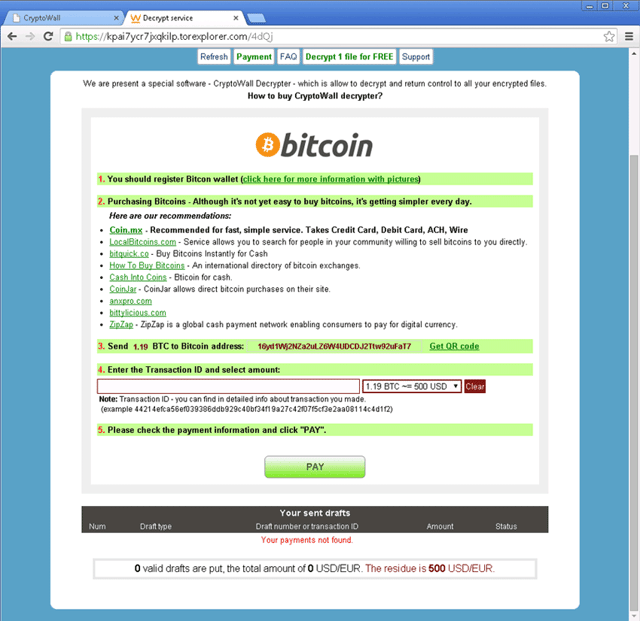
The cyber criminals behind CryptoDefense released an improved version called CryptoWall. While largely similar to the earlier edition, CryptoWall doesn’t store the encryption key where the user can get to it. In addition, while CryptoDefense required the user to open an infected attachment, CryptoWall uses a Java vulnerability. Malicious advertisements on domains belonging to Disney, Facebook, The Guardian newspaper and many others led people to sites that were CryptoWall infected and encrypted their drives. According to an August 27 report from Dell SecureWorks Counter Threat Unit (CTU): “CTU researchers consider CryptoWall to be the largest and most destructive ransomware threat on the Internet as of this publication, and they expect this threat to continue growing.” More than 600,000 systems were infected between mid-March and August 24, with 5.25 billion les being encrypted. 1,683 victims (0.27%) paid a total $1,101,900 in ransom. Nearly 2/3 paid $500, but the amounts ranged from $200 to $10,000.
For the most part, CryptoWall has been in the shadows of its predecessor CryptoLocker, but since its takedown by the FBI CryptoWall has taken over the reigns as the newest threat on the block.
CryptoWall is facilitated via emails with ZIP attachments where the virus is hidden as PDF files. The PDF files often disguise themselves as bills, purchase orders, invoices, and etc. When victims open the malicious PDF files, they infect the computer with the CryptoWall virus and install malware files either in the %AppData% or %Temp% folders. CryptoWall 4.0 is now delivered via the Nuclear Exploit Kit, (NEK) as well. Once the computer is infected the installer will start to snoop around the computer’s drives for data files that it can encrypt. Finally, when the virus is scanning the computer it will locate drive letters on the PC including network shares, Dropbox mappings, and removable drivers. In short, if there are any drive letters present on your computer CryptoWall will scan it for data files. What makes CryptoWall different is it is coded to run on both 32-bit and 64-bit systems, that increase chances of the virus running on whatever computer it happens to infect. Newer versions of Mac OS X and Windows are 64-bit operating systems that can be vulnerable to such attacks.
Furthermore, CryptoWall in its diabolical savviness utilizes strong public-key cryptography to distort files with specific extensions. Unlike other ransomware viruses, paying a ransom is not the only option that victims have. By restoring files from a backup, they may be able to thwart the attack, unless of course CyrptoWall is able to find those as well. A good solution to backing up files is to use a portable backup drive.
