8. Contact your insurance company
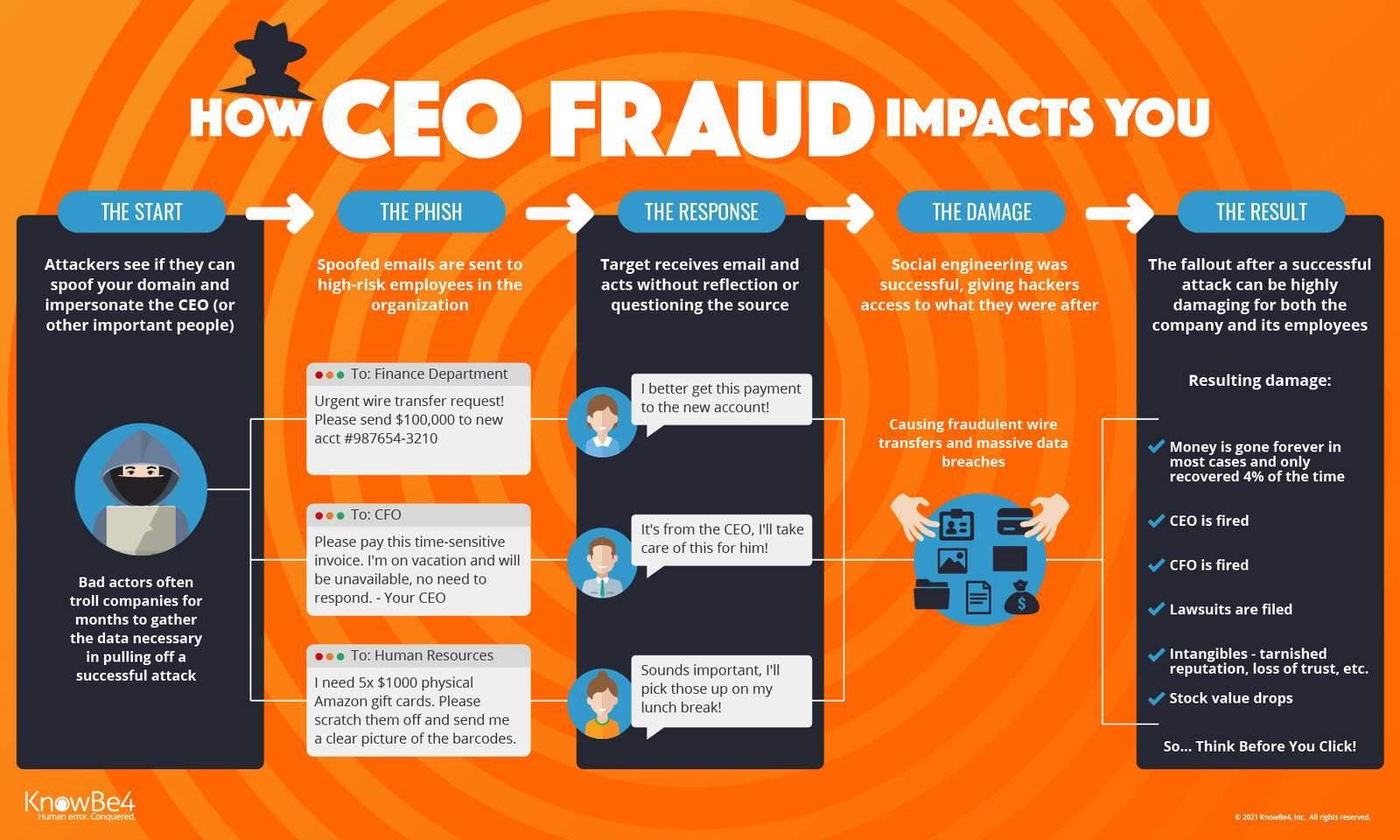
Make sure your cybersecurity insurance covers CEO Fraud: Less than 4% of fraudulently transferred funds are recovered, so it's a good idea to make sure you have the proper insurance in place. While many organizations have taken out cyber-insurance, not all are specifically covered in the event of CEO fraud. This is a grey area in insurance and many refuse to pay up. Despite the presence of a specific cyber insurance policy, the unfortunate fact is that no hardware or software was hacked. It was the human that was hacked instead.
Difference between financial instruments and email fraud: Insurance companies distinguish between these two and that's where gray areas come in. Financial instruments can be defined as monetary contracts between parties such as cash (currency), evidence of an ownership interest in an entity (share), or a contractual right to receive or deliver cash (bond). However, CEO fraud is often categorized as being purely an email fraud and not a financial instrument fraud. In other words, it is being regarded in many cases as a matter of internal negligence or email impersonation as opposed to being a financial instrument matter.
That said, there are dozens of carriers in the market providing up to $300 million in limits. Coverage extensions have developed to include both the third-party liability and first-party cost and expenses associated with a data breach or cyber-attack.